OWASP Internet of Things

The OWASP Internet of Things Project is designed to help manufacturers, developers, and consumers better understand the security issues associated with the Internet of Things, and to enable users in any context to make better security decisions when building, deploying, or assessing IoT technologies.
The project looks to define a structure for various IoT sub-projects separated into the following categories - Seek & Understand, Validate & Test, and Governance. Right now, you can find the following active and upcoming OWASP Internet of Things projects:
Internet of Things Page Archive
Not what you are looking for? Please have a look at the Internet of Things Page Archive.
Start a new IoT security project
Want to start a new IoT security project? Follow https://www.owasp.org/index.php/Category:OWASP_Project#Starting_a_New_Project or contact one of the leaders of the active projects.
Seek & Understand
IoT Top 10
Project Leader(s)
- Daniel Miessler
- Aaron Guzman
- Vishruta Rudresh
- Craig Smith
Description
Top ten things to avoid when building, deploying or managing IoT systems.
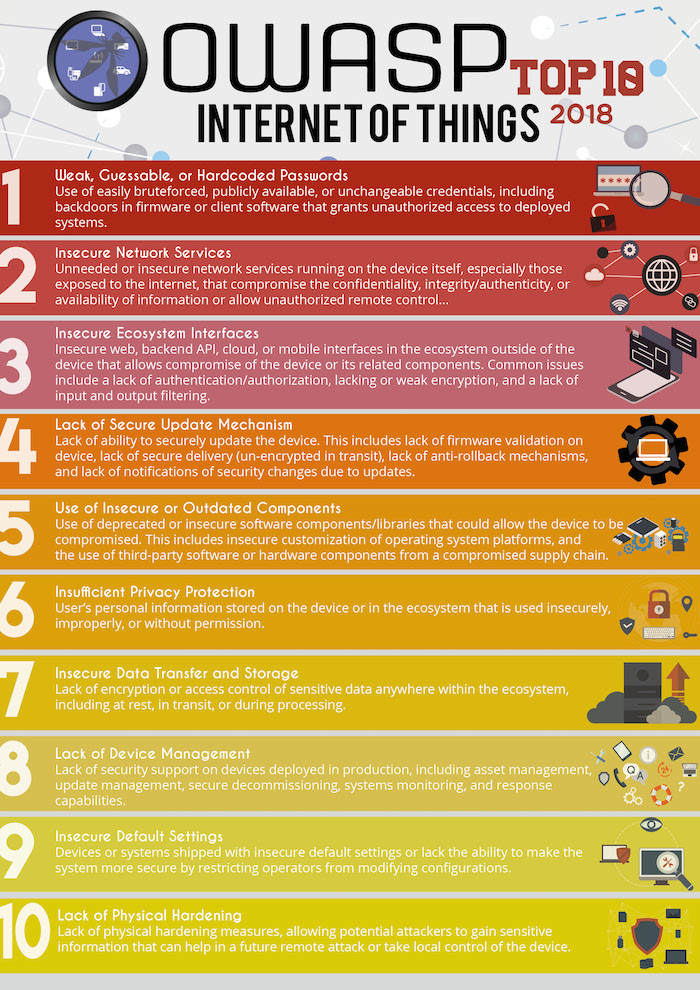
| OWASP IoT Top 10 2018 | Description |
|---|---|
| I1 Weak, Guessable, or Hardcoded Passwords | Use of easily bruteforced, publicly available, or unchangeable credentials, including backdoors in firmware or client software that grants unauthorized access to deployed systems. |
| I2 Insecure Network Services | Unneeded or insecure network services running on the device itself, especially those exposed to the internet, that compromise the confidentiality, integrity/authenticity, or availability of information or allow unauthorized remote control. |
| I3 Insecure Ecosystem Interfaces | Insecure web, backend API, cloud, or mobile interfaces in the ecosystem outside of the device that allows compromise of the device or its related components. Common issues include a lack of authentication/authorization, lacking or weak encryption, and a lack of input and output filtering. |
| I4 Lack of Secure Update Mechanism | Lack of ability to securely update the device. This includes lack of firmware validation on device, lack of secure delivery (un-encrypted in transit), lack of anti-rollback mechanisms, and lack of notifications of security changes due to updates. |
| I5 Use of Insecure or Outdated Components | Use of deprecated or insecure software components/libraries that could allow the device to be compromised. This includes insecure customization of operating system platforms, and the use of third-party software or hardware components from a compromised supply chain |
| I6 Insufficient Privacy Protection | User’s personal information stored on the device or in the ecosystem that is used insecurely, improperly, or without permission. |
| I7 Insecure Data Transfer and Storage | Lack of encryption or access control of sensitive data anywhere within the ecosystem, including at rest, in transit, or during processing |
| I8 Lack of Device Management | Lack of security support on devices deployed in production, including asset management, update management, secure decommissioning, systems monitoring, and response capabilities. |
| I9 Insecure Default Settings | Devices or systems shipped with insecure default settings or lack the ability to make the system more secure by restricting operators from modifying configurations. |
| I10 Lack of Physical Hardening | Lack of physical hardening measures, allowing potential attackers to gain sensitive information that can help in a future remote attack or take local control of the device. |
IoT Top 10 Mapping Project
Project Leader(s)
- Aaron Guzman
- José A. Rivas
Description
Provides mappings of the OWASP IoT Top 10 2018 to industry publications and sister projects.
| OWASP IoT Top 10 2014 | OWASP IoT Top 10 2018 Mapping |
|---|---|
| I1 Insecure Web Interface | I3 Insecure Ecosystem Interfaces |
| I2 Insufficient Authentication/Authorization | I1 Weak, Guessable, or Hardcoded Passwords I3 Insecure Ecosystem Interfaces I9 Insecure Default Settings |
| I3 Insecure Network Services | I2 Insecure Network Services |
| I4 Lack of Transport Encryption/Integrity Verification | I7 Insecure Data Transfer and Storage |
| I5 Privacy Concerns | I6 Insufficient Privacy Protection |
| I6 Insecure Cloud Interface | I3 Insecure Ecosystem Interfaces |
| I7 Insecure Mobile Interface | I3 Insecure Ecosystem Interfaces |
| I8 Insufficient Security Configurability | I9 Insecure Default Settings |
| I9 Insecure Software/Firmware | I4 Lack of Secure Update Mechanism I5 Use of Insecure or Outdated Components |
| I10 Poor Physical Security | I10 Lack of Physical Hardening |
IoTGoat
Project Leader(s)
- Aaron Guzman
- Fotios Chantzis
- Paulino Calderon
Description
IoTGoat is a deliberately insecure firmware based on OpenWrt. The project’s goal is to teach users about the most common vulnerabilities typically found in IoT devices. The vulnerabilities will be based on the top 10 vulnerabilities as documented by OWASP: https://wiki.owasp.org/index.php/OWASP_Internet_of_Things_Project.
Releases
- OWASP IoTGoat v1.0 is out! Please send us your feedback!

Validate & Test
OWASP IoT Security Testing Guide (ISTG)
Project Leader(s)
- Luca Rotsch
- Aaron Guzman
Description
The OWASP IoT Security Testing Guide provides a comprehensive methodology for penetration tests in the IoT field offering flexibility to adapt innovations and developments on the IoT market while still ensuring comparability of test results. The guide provides an understanding of communication between manufacturers and operators of IoT devices as well as penetration testing teams that’s facilitated by establishing a common terminology.
The methodology, the underlying models and the catalog of test cases present tools that can be used separately and in conjunction with each other.
Check out the projects GitHub for more details: https://github.com/OWASP/owasp-istg
Firmware Security Testing Methodology (FSTM)
Project Leader(s)
- Aaron Guzman
Description
The Firmware Security Testing Methodology (FSTM) is composed of nine stages tailored to enable security researchers, software developers, consultants, hobbyists, and Information Security professionals with conducting firmware security assessments.
| Stage | Description |
|---|---|
| 1. Information gathering and reconnaissance | Acquire all relative technical and documentation details pertaining to the target device’s firmware |
| 2. Obtaining firmware | Attain firmware using one or more of the proposed methods listed |
| 3. Analyzing firmware | Examine the target firmware’s characteristics |
| 4. Extracting the filesystem | Carve filesystem contents from the target firmware |
| 5. Analyzing filesystem contents | Statically analyze extracted filesystem configuration files and binaries for vulnerabilities |
| 6. Emulating firmware | Emulate firmware files and components |
| 7. Dynamic analysis | Perform dynamic security testing against firmware and application interfaces |
| 8. Runtime analysis | Analyze compiled binaries during device runtime |
| 9. Binary Exploitation | Exploit identified vulnerabilities discovered in previous stages to attain root and/or code execution |
ByteSweep
Project Leader(s)
- Matt Brown
Description
ByteSweep is a Free Software IoT security analysis platform. This platform will allow IoT device makers, large and small, to conduct fully automated security checks before firmware is shipped.
Firmware Analysis Project (Archived)
Project Leader(s)
- Craig Smith
Description
The Firmware Analysis Project provides: Security testing guidance for vulnerabilities in the “Device Firmware” attack surface, Steps for extracting file systems from various firmware files, Guidance on searching a file systems for sensitive of interesting data, Information on static analysis of firmware contents, Information on dynamic analysis of emulated services (e.g. web admin interface), Testing tool links, and a site for pulling together existing information on firmware analysis
Governance
Catalogue of IoT regulatory policies and Certifications
Project Leader(s)
- TBD
Description
TBD